Introduction
In the ever-evolving world of technology, the ability to seamlessly transfer data between a host system and various attached devices has become a crucial aspect of modern computing. Whether it’s a desktop computer communicating with peripherals, a mobile device synchronizing with accessories, or an industrial control system managing multiple sensors and actuators, efficient data transfer protocols play a pivotal role in ensuring smooth and reliable operations.
This article delves into the intricate realm of data transfer protocols, exploring their significance, functionalities, and the diverse range of applications they enable. We’ll unravel the complexities of these protocols, shedding light on their underlying mechanisms, and examine how they facilitate the exchange of information between a host and its connected devices.
Understanding Data Transfer Protocols
Data transfer protocols are a set of rules and conventions that govern how data is transmitted and received between two or more systems. These protocols define the format, structure, and sequence of the data being exchanged, ensuring that the information is delivered accurately and efficiently.
At the heart of these protocols lies a standardized framework that establishes a common language for communication. By adhering to these predefined rules, devices from different manufacturers can seamlessly interact and exchange data, enabling interoperability and promoting a seamless ecosystem of interconnected devices.
Importance of Data Transfer Protocols
The significance of data transfer protocols cannot be overstated, as they play a crucial role in various aspects of modern computing and technology:
- Interoperability: Protocols enable devices from different manufacturers to communicate and exchange data, fostering an ecosystem of interconnected systems and promoting device compatibility.
- Reliable Data Transfer: Protocols incorporate error-checking mechanisms and data integrity measures to ensure that data is transmitted accurately and without corruption, minimizing the risk of data loss or corruption during transmission.
- Efficient Communication: Well-designed protocols optimize the use of available bandwidth and system resources, enabling efficient data transfer and reducing latency, which is particularly crucial in time-sensitive applications.
- Standardization: Widely adopted protocols promote standardization, simplifying the development and integration of new devices and systems, as well as facilitating compatibility across different platforms and environments.
- Security: Many protocols incorporate security features, such as encryption and authentication mechanisms, to protect sensitive data from unauthorized access or tampering during transmission.
Types of Data Transfer Protocols
The world of data transfer protocols is diverse, with various protocols designed to cater to different needs and scenarios. Here are some of the most commonly used protocols:
1. Universal Serial Bus (USB)
USB is a widely adopted protocol for connecting peripheral devices to a host computer or device. It provides a standardized interface for data transfer, power delivery, and device communication. USB supports a wide range of devices, including storage devices, printers, cameras, and input devices.
2. Bluetooth
Bluetooth is a wireless protocol that enables short-range communication between devices. It is widely used for connecting various accessories, such as headphones, speakers, keyboards, and mice, to a host device like a smartphone, tablet, or computer.
3. Wi-Fi
Wi-Fi is a wireless networking protocol that allows devices to connect to a local area network (LAN) or the internet. It facilitates data transfer between devices within a certain range, enabling wireless communication and internet access.
4. Ethernet
Ethernet is a wired networking protocol that enables devices to connect to a local area network (LAN) or wide area network (WAN). It is widely used in office and home environments for connecting computers, printers, and other networked devices.
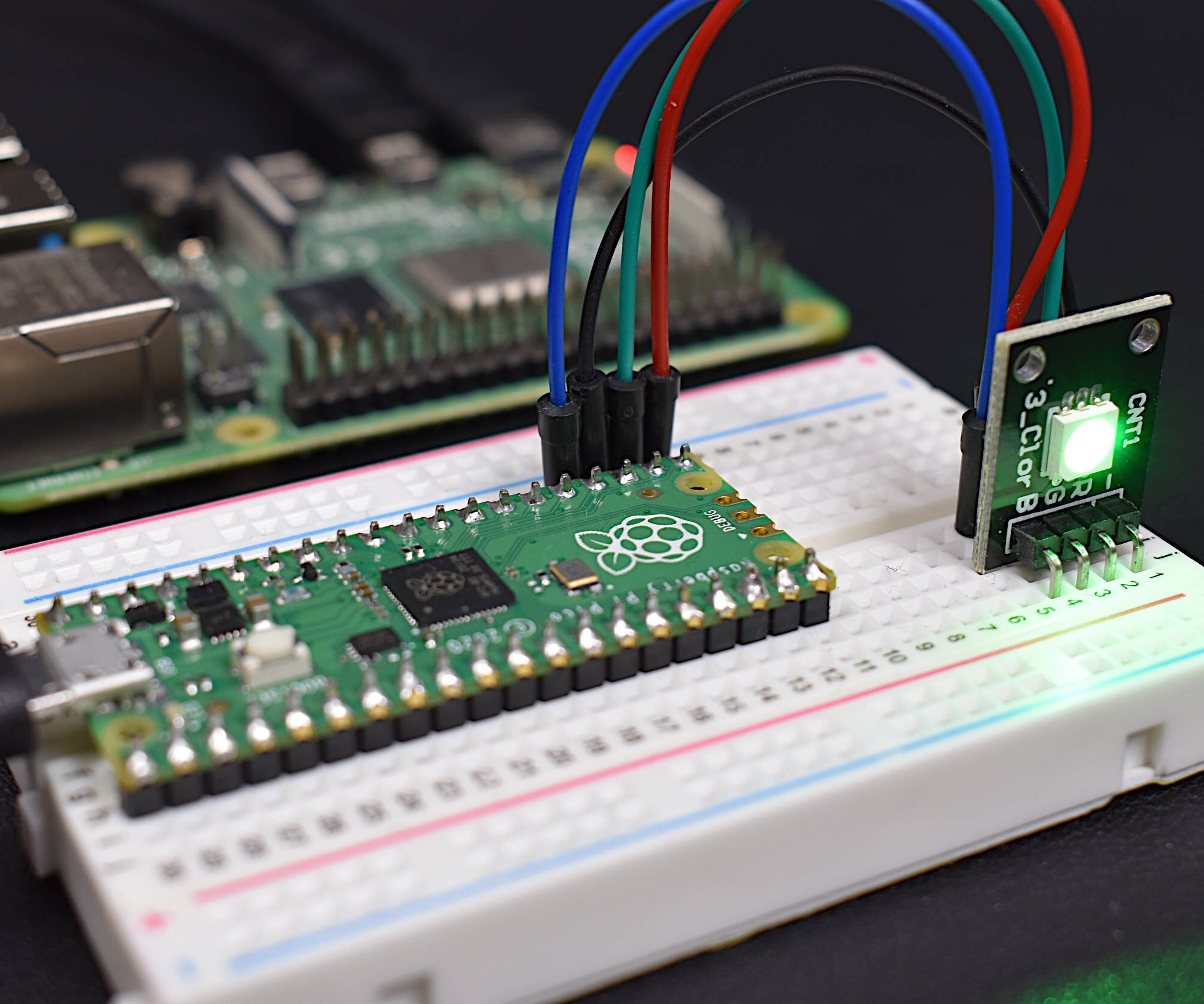
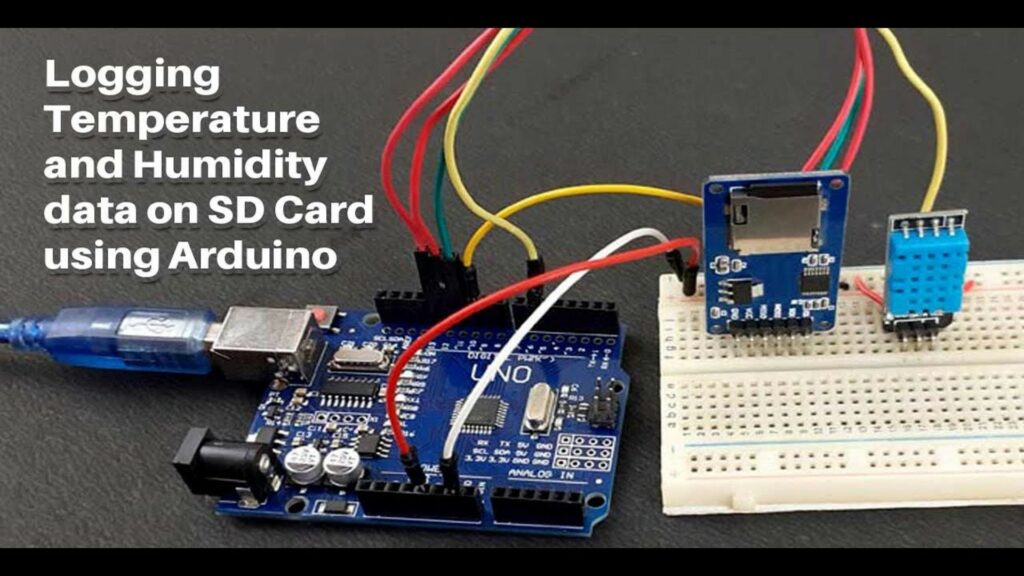
5. Serial Communication Protocols (UART, SPI, I2C)
Serial communication protocols, such as UART (Universal Asynchronous Receiver-Transmitter), SPI (Serial Peripheral Interface), and I2C (Inter-Integrated Circuit), are commonly used for communication between microcontrollers, sensors, and other embedded devices. These protocols enable data exchange over a single or multiple wires, making them suitable for low-speed, low-power applications.
6. Internet Protocols (TCP/IP, HTTP, FTP)
Internet protocols, such as TCP/IP (Transmission Control Protocol/Internet Protocol), HTTP (Hypertext Transfer Protocol), and FTP (File Transfer Protocol), govern data transfer over the internet and wide area networks. These protocols enable communication between web servers and clients, facilitating activities like web browsing, file transfers, and online transactions.
7. Industrial Protocols (Modbus, CAN, PROFIBUS)
Industrial protocols, such as Modbus, CAN (Controller Area Network), and PROFIBUS, are designed for communication in industrial automation and control systems. These protocols enable reliable data exchange between programmable logic controllers (PLCs), sensors, actuators, and other industrial equipment, ensuring efficient and secure operations in manufacturing and process control environments.
Factors Influencing Protocol Selection
When selecting a data transfer protocol, several factors must be considered to ensure optimal performance and suitability for the intended application:
- Data Transfer Rate: Different protocols offer varying data transfer rates, ranging from low-speed serial communication to high-speed networking protocols. The required data transfer rate is a critical factor in protocol selection, as it directly impacts performance and responsiveness.
- Range and Connectivity: Some protocols are designed for short-range communication, while others support long-range data transfer over wired or wireless networks. The desired range and connectivity requirements, such as wired or wireless, play a significant role in protocol choice.
- Power Consumption: In battery-powered or energy-constrained devices, power consumption is a crucial consideration. Protocols with lower power requirements may be preferred in such scenarios to extend battery life and reduce energy consumption.
- Security Requirements: Depending on the application and the sensitivity of the data being transferred, security may be a critical factor. Protocols with built-in encryption and authentication mechanisms may be necessary to protect data from unauthorized access or tampering.
- Compatibility and Interoperability: Ensuring compatibility and interoperability with existing systems, devices, and infrastructure is essential when selecting a data transfer protocol. Widely adopted standards and protocols are often preferred to facilitate seamless integration and communication.
- Reliability and Error Handling: Certain applications may require robust error handling and reliable data transfer mechanisms. Protocols with built-in error detection and correction features may be necessary to ensure data integrity and minimize the risk of data loss or corruption.
- Cost and Licensing: The cost of implementing and licensing a particular protocol can be a factor, especially in large-scale deployments or resource-constrained environments. Open and royalty-free protocols may be preferred in such cases.
By carefully evaluating these factors and considering the specific requirements of the application, developers and system integrators can make informed decisions when selecting the most appropriate data transfer protocol.
Implementing Data Transfer Protocols
The implementation of data transfer protocols involves several key components and considerations:
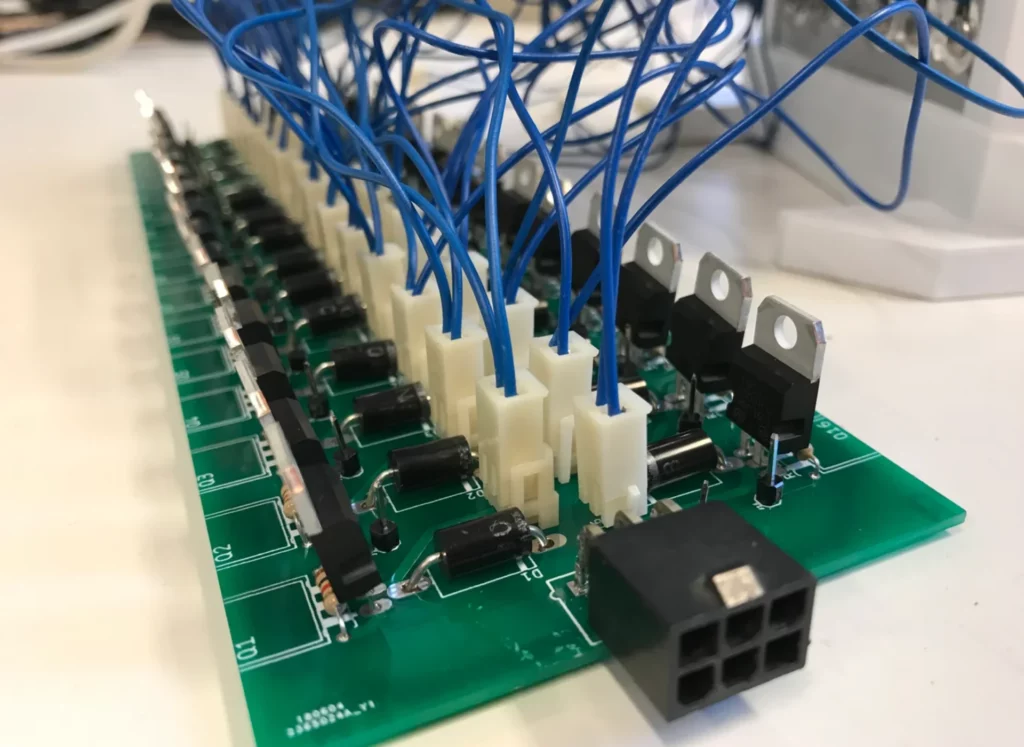
1. Hardware Support
Many protocols require hardware support in the form of dedicated interface chips, transceivers, or integrated circuits. These hardware components facilitate the physical layer communication and ensure compliance with the protocol specifications.
2. Software Libraries and Drivers
Software libraries and drivers are essential for enabling communication between the host system and the attached devices. These software components provide a high-level abstraction layer, simplifying the implementation and handling of protocol-specific details.
3. Protocol Stack
Most data transfer protocols are organized into a hierarchical stack, with each layer responsible for specific functions and services. The protocol stack ensures proper encapsulation, sequencing, and interpretation of data during transmission and reception.
4. Error Handling and Recovery
Robust error handling and recovery mechanisms are crucial for ensuring reliable data transfer. Protocols often incorporate techniques such as error detection codes, retransmission strategies, and flow control mechanisms to mitigate the impact of errors and maintain data integrity.
5. Security Considerations
Depending on the protocol and the application requirements, security measures may need to be implemented to protect data during transmission. These measures can include encryption, authentication, and access control mechanisms to prevent unauthorized access, data tampering, or eavesdropping.
6. Testing and Validation
Thorough testing and validation are essential to ensure the correct implementation and interoperability of data transfer protocols. This may involve conformance testing, interoperability testing, and performance benchmarking to verify compliance with protocol specifications and identify potential issues or bottlenecks.
7. Documentation and Support
Clear and comprehensive documentation is crucial for developers and integrators working with data transfer protocols. This documentation should cover protocol specifications, implementation guidelines, best practices, and troubleshooting information. Additionally, access to community support, forums, and developer resources can greatly aid in resolving issues and gaining insights from experienced users.
By carefully addressing these implementation aspects, developers and system integrators can ensure reliable, efficient, and secure data transfer between the host and various attached devices, enabling seamless communication and interoperability within the connected ecosystem.
Applications of Data Transfer Protocols
Data transfer protocols are ubiquitous in our modern technological landscape, enabling a vast array of applications across various industries and domains. Here are some notable examples:
1. Consumer Electronics
Consumer electronics, such as smartphones, tablets, laptops, and smart home devices, rely heavily on data transfer protocols to communicate with peripherals and accessories. USB, Bluetooth, and Wi-Fi protocols facilitate seamless integration and data exchange between these devices and their respective ecosystems.
2. Industrial Automation and Control Systems
Industrial protocols like Modbus, CAN, and PROFIBUS are essential for enabling communication between programmable logic controllers (PLCs), sensors, actuators, and other industrial equipment in manufacturing and process control environments. These protocols ensure reliable and efficient data transfer, enabling real-time monitoring, control, and automation of industrial processes.
3. Networking and Internet Communication
Internet protocols, such as TCP/IP, HTTP, and FTP, are the backbone of modern communication and data transfer over the internet and wide area networks. These protocols enable activities like web browsing, file transfers, online transactions, and cloud computing services, facilitating global connectivity and information exchange.
4. Automotive and Transportation Systems
In the automotive industry, protocols like CAN and FlexRay are used for in-vehicle communication, enabling the exchange of data between various electronic control units (ECUs) responsible for functions such as engine management, braking systems, and infotainment systems.
5. Healthcare and Medical Devices
Data transfer protocols play a crucial role in the healthcare industry, facilitating communication between medical devices, patient monitoring systems, and hospital information systems. Protocols like HL7 (Health Level 7) and DICOM (Digital Imaging and Communications in Medicine) ensure seamless data exchange and interoperability, enabling efficient patient care and data management.
6. Scientific and Research Applications
In scientific and research fields, protocols like Ethernet, USB, and serial communication protocols are widely used for connecting and controlling laboratory equipment, data acquisition systems, and scientific instruments. These protocols enable efficient data collection, analysis, and collaboration among researchers and scientists.
7. Embedded Systems and Internet of Things (IoT)
The Internet of Things (IoT) relies heavily on data transfer protocols for enabling communication between embedded devices, sensors, and gateways. Protocols like Wi-Fi, Bluetooth Low Energy (BLE), and various low-power wireless protocols facilitate data exchange, remote monitoring, and control in IoT applications across industries such as smart homes, industrial automation, and urban infrastructure management.
These examples illustrate the pervasive nature of data transfer protocols and their critical role in enabling seamless communication, interoperability, and data exchange across a wide range of applications and industries.
Frequently Asked Questions (FAQ)
- What is the difference between serial and parallel data transfer protocols? Serial protocols transmit data one bit at a time over a single communication channel, while parallel protocols transfer multiple bits simultaneously over multiple parallel channels. Serial protocols are commonly used for low-speed communication, while parallel protocols are often employed for high-speed data transfer.
- Why are data transfer protocols important for interoperability? Data transfer protocols establish a common set of rules and conventions for communication, enabling devices from different manufacturers to exchange data seamlessly. By adhering to these standardized protocols, devices can communicate and interact with each other, fostering an ecosystem of interoperable systems and promoting device compatibility.
- How do data transfer protocols ensure reliable data transfer? Many data transfer protocols incorporate error-checking mechanisms and data integrity measures to ensure that data is transmitted accurately and without corruption. These measures may include cyclic redundancy checks (CRC), checksums, or other error detection and correction techniques. Additionally, protocols often implement retransmission strategies and flow control mechanisms to mitigate the impact of errors and maintain data integrity.
- What are the key factors to consider when selecting a data transfer protocol? Several factors should be considered when selecting a data transfer protocol, including the required data transfer rate, range and connectivity requirements (wired or wireless), power consumption constraints, security needs, compatibility and interoperability with existing systems, reliability and error handling requirements, and cost and licensing considerations.
- How do data transfer protocols ensure secure communication? Many data transfer protocols incorporate security features to protect sensitive data during transmission. These features may include encryption mechanisms to scramble the data and prevent unauthorized access, authentication protocols to verify the identity of communicating parties, and access control mechanisms to restrict access to authorized entities only. Protocols like SSL/TLS, IPsec, and WPA2 are examples of protocols with built-in security features.
By understanding the fundamentals of data transfer protocols, their importance, types, and applications, developers, system integrators, and end-users can make informed decisions and leverage these protocols effectively to enable seamless communication and data exchange between the host and various attached devices.